Cybersecurity Maturity Model Certification (CMMC): A Practical Guide for Defense Contractors
Cybersecurity has become a major focus for the Department of Defense (DoD), especially as cyber threats targeting the Defense Industrial Base (DIB) continue to grow in frequency and complexity. To address these risks, the DoD developed the Cybersecurity Maturity Model Certification (CMMC) program. The goal of CMMC is straightforward: verify that contractors working with the Department of Defense are properly protecting sensitive government information. If your organization handles government contract data - especially Federal Contract Information (FCI) or Controlled Unclassified Information (CUI)- you will likely need to meet CMMC requirements in order to win or maintain certain DoD contracts.
What Is the Cybersecurity Maturity Model Certification (CMMC)?
The Cybersecurity Maturity Model Certification (CMMC) is a cybersecurity verification program created by the Department of Defense (DoD) to strengthen security across its contractor network. Instead of relying entirely on contractors to self-attest that they meet cybersecurity requirements, CMMC introduces structured assessments to confirm that security controls are actually in place. In practical terms, CMMC ensures that companies handling sensitive defense information follow established cybersecurity standards and maintain those protections throughout the life of a contract with the DoD.
Organizations may need CMMC certification if they:
- Work as a DoD contractor or subcontractor
- Store, process, or transmit Federal Contract Information (FCI)
- Handle Controlled Unclassified Information (CUI)
The full, most-current details of the CMMC requirements are available on the DOD website at dodcio.defense.gov/CMMC/.
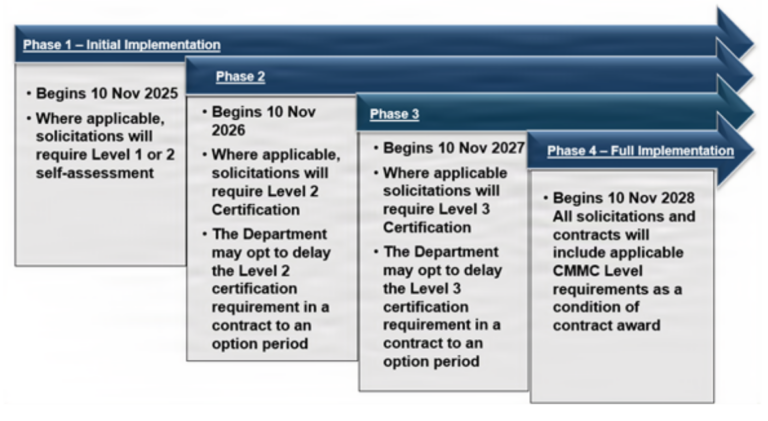
CMMC Implementation Timeline
The Cybersecurity Maturity Model Certification program began phased implementation on November 10, 2025. The Department of Defense is rolling out the program through four phases over approximately three years. This phased rollout gives contractors time to prepare their cybersecurity programs, assessors time to complete certification training, and the DoD time to gradually incorporate requirements into contracts
Types of Information Protected by CMMC
The CMMC framework focuses on protecting two primary types of government information. Understanding the difference between them is important because it often determines the certification level your organization needs.
Federal Contract Information (FCI)
Federal Contract Information (FCI) refers to information that is generated for or provided by the government as part of a federal contract and is not intended for public release. Examples of FCI may include Contract specifications, Internal project communications, and/or Technical documentation related to contract work. However, publicly available information or simple administrative data (such as payment processing information) is not considered FCI.
Controlled Unclassified Information (CUI)
Controlled Unclassified Information (CUI) is a category of sensitive information that requires protection but is not classified. CUI can include information such as Engineering drawings, Defense program documentation, and/or Sensitive operational data. Government policy requires organizations handling CUI to implement stronger cybersecurity controls. Because of this, contractors dealing with CUI generally need to meet higher CMMC certification levels.
Key Features of the CMMC Program
The Cybersecurity Maturity Model Certification program introduces several structural changes to how cybersecurity compliance works within the defense supply chain. These changes are designed to improve visibility, accountability, and consistency across contractors.
A Tiered Certification Model
CMMC uses a tiered system of certification levels, each representing progressively stronger cybersecurity practices. The level your organization must achieve depends on the type and sensitivity of the information you handle. This structure allows the Department of Defense to apply cybersecurity requirements based on actual risk.
Cybersecurity Assessments
A core part of the CMMC framework is the use of cybersecurity assessments. These assessments confirm that contractors have implemented the required security controls. Depending on the certification level, assessments may be self-assessments performed internally, or third-party assessments conducted by certified organizations. The goal is to move beyond paper compliance and ensure cybersecurity practices are actually functioning in the contractor’s environment.
Certification Requirements in Contracts
Under the Cybersecurity Maturity Model Certification program, certification is tied directly to defense contracts. This means contractors must meet the required CMMC level before receiving certain DoD contract awards. Additionally, CMMC requirements can flow down to subcontractors if they also handle FCI or CUI. For many organizations, this means cybersecurity compliance is no longer optional it is a part of doing business with the Department of Defense.
CMMC Certification Levels Explained
The Cybersecurity Maturity Model Certification framework currently includes three certification levels. Each level corresponds to different cybersecurity expectations and information protection requirements.
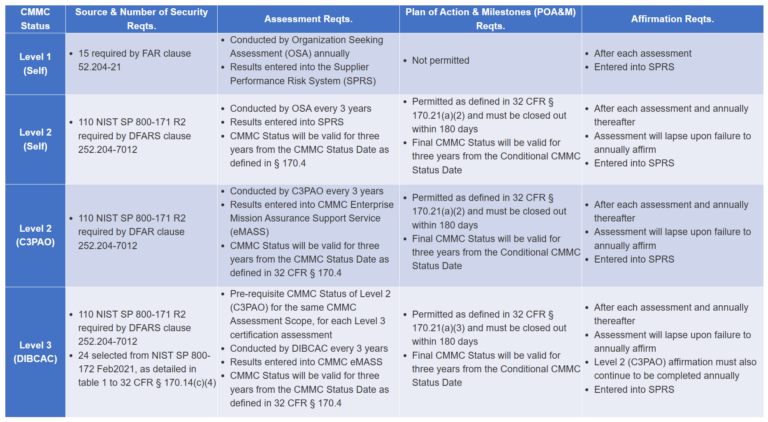
CMMC Level 1: Basic Safeguarding of Federal Contract Information
CMMC Level 1 focuses on protecting Federal Contract Information. To meet Level 1 requirements, organizations must perform an annual self-assessment, submit an annual compliance affirmation, and implement 15 security controls outlined in FAR 52.204-21. These controls establish basic cybersecurity practices such as limiting system access, protecting devices, and safeguarding information systems. For many small contractors entering the defense supply chain, Level 1 is the starting point for CMMC compliance.
CMMC Level 2: Protection of Controlled Unclassified Information
CMMC Level 2 is required for contractors that handle Controlled Unclassified Information. This level aligns with the cybersecurity standards found in NIST SP 800-171. Organizations seeking Level 2 certification must implement 110 security controls, conduct an assessment every three years, and provide annual compliance affirmations. Depending on contract requirements, the assessment may be a self-assessment, or an independent assessment by a CMMC Third-Party Assessment Organization (C3PAO).
CMMC Level 3: Protection Against Advanced Cyber Threats
CMMC Level 3 is intended for contractors supporting highly sensitive defense programs. This level adds additional security measures designed to protect against Advanced Persistent Threats (APTs). To achieve Level 3 certification, organizations must achieve Final Level 2 status, undergo assessments every three years, be assessed by the Defense Contract Management Agency (DCMA) DIBCAC, and implement additional security requirements from NIST SP 800-172.